The COVID-19 pandemic and the sweeping shutdowns to contain the spread of the virus brought about significant impacts on businesses. Many small companies realized they lacked the resources to rapidly adopt a remote work setup and tapped their IT partners to help address their technology demands.
How MSPs are supporting clients during the COVID-19 pandemic
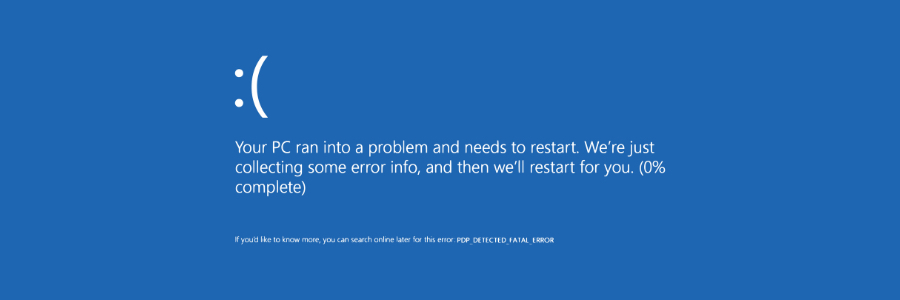
Why the latest Windows 10 update is blocked on some PCs
VoLTE: What is it, and how different is it from VoIP?

Voice over Internet Protocol (VoIP) is a must for today’s businesses. Compared to the old analog phone system, VoIP is a more effective communication tool. Aside from making voice calls, you can also do conference calls, send instant messaging, queue calls, have music on hold, and record calls with VoIP. But now there’s a new technology called Voice over Long-Term Evolution (VoLTE). How different are the two from each other, and is VoLTE poised to take over VoIP?
To know the difference between VoIP and VoLTE, let’s first examine the older of the two technologies.
Microsoft 365 update channels: What you need to know
Why your SMB needs a business continuity plan (BCP)

Multiple things can disrupt the operations of small- to medium-sized businesses (SMBs), such as natural disasters or cyberattacks. This can lead to lost revenue, or in some extreme cases, business closure. But having a concrete business continuity plan (BCP) in place will help your business recover quickly after a disaster.
New Windows 10 update: Things you need to know

The Windows 10 update will roll out on May 26–28, 2020 and will bring about a fresher look for the world’s most popular operating system. Aside from updates to Windows 10’s interface, here are some functionality improvements you can expect.
The update — named Windows 10 20H1/Windows 10 version 2004 — will feature some performance-enhancing upgrades and an initial rollout of new designs.
Why you should consider softphones over desk phones
Desk phones that sit in the office are quickly becoming obsolete as many employees work off-site. Instead of traditional telephony systems, forward-thinking businesses are using softphones for most, if not all, of their communications. If your company hasn’t already done so, here are five compelling reasons why you need to start using softphones.
Office 365 is now Microsoft 365: New features, same price

Microsoft recently launched its new slate of consumer service plans: Microsoft 365 (M365) Personal and Family. This will replace Office 365 (O365) Home and Personal, signaling the shift of the company’s consumer bundles from just a set of tools to powerful solutions that help you manage both work and life.
5 Tips to keep your business afloat during the COVID-19 crisis

Businesses across the globe have been hit hard by the COVID-19 pandemic. Many have been forced to close their doors, some only temporarily, but countless others for good. With experts saying there’s no guarantee of a rapid economic recovery, it’s important that you reassess and redefine your business strategy and buckle down for more storms ahead.